Hidden Risks of Unprotected Online Calendar Sharing
In today’s digital world, sharing calendars online has become a common practice for coordinating schedules and events. However, this convenience comes with serious hidden risks that many users overlook. Unprotected calendar sharing can expose sensitive information, making it vulnerable to hackers and cybercriminals. For instance, details like meeting times, locations, and personal notes might reveal your daily routine or even financial habits. This exposure increases the chances of identity theft and targeted attacks. People often assume that online calendars are secure, but without proper encryption, they become easy targets for data breaches. SEO experts recommend using strong passwords and privacy settings to mitigate these threats. As more individuals rely on tools like Google Calendar or Outlook, understanding these risks is crucial for protecting your digital life. The potential consequences include not only privacy invasions but also reputational damage from leaked information. Therefore, it’s essential to evaluate your online habits and adopt better security measures. By doing so, you can enjoy the benefits of calendar sharing without compromising your safety. This post will explore three key risks in detail, helping you make informed decisions about your online activities.

Exposure of Personal Data
Unprotected calendars often leak personal details to unauthorized viewers. For example, shared events might include addresses or phone numbers. This risk affects everyone from professionals to families. Hackers can exploit this information for scams or stalking. Moreover, public links make it simple for anyone to access your schedule. Businesses face additional threats, as corporate calendars could reveal confidential meetings. Therefore, everyday users must be cautious about sharing options. Social engineering attacks frequently target these vulnerabilities. You might think private settings suffice, but many platforms have flaws. Thus, regular audits of your calendar permissions are necessary. Additionally, integrating two-factor authentication adds another layer of protection. Without these steps, your data remains at risk. In fact, studies show that over 60% of breaches involve human error, like improper sharing. Consequently, educating yourself on best practices is vital. Tools that automatically hide sensitive entries can help mitigate issues. Overall, the exposure of personal data through calendars is a widespread problem that demands immediate attention.
Vulnerability to Cyber Attacks

Cyber attacks on unprotected calendars are increasingly common in the digital age. For instance, malware can infiltrate shared links and steal information. This threat impacts users across all demographics, from students to executives. Attackers often use phishing to gain access to calendars. Therefore, recognizing suspicious emails is a key defense. Moreover, unencrypted data transmissions make calendars easy targets for interception. Hackers might then use this data for ransomware demands. In addition, weak passwords exacerbate the problem, allowing brute-force attacks. Consequently, updating security protocols regularly is essential. Many popular calendar apps have faced breaches, highlighting the need for vigilance. For example, a single compromised account can lead to widespread data loss. Thus, employing antivirus software alongside calendar use is advisable. The financial cost of such attacks can be substantial, including lost productivity. Furthermore, personal safety is at stake if locations are exposed. Overall, vulnerability to cyber attacks underscores the importance of robust online protection.
Risks of Identity Theft

Identity theft through unprotected calendars poses a severe danger to individuals. For example, shared schedules can reveal patterns that thieves exploit for fraud. This issue affects anyone with an online presence, including casual users. Thieves might use event details to impersonate you online. Therefore, minimizing shared information is crucial. Moreover, combining calendar data with social media amplifies the risks. Attackers can piece together a full profile from these sources. In fact, identity theft cases linked to calendar leaks have risen sharply. Consequently, using anonymous sharing features can reduce exposure. Financial institutions warn that such breaches often lead to unauthorized transactions. Additionally, protecting your calendar helps safeguard your credit history. Thus, implementing encryption tools is a smart move. Everyday precautions, like avoiding public links, make a difference. Furthermore, monitoring your accounts for unusual activity is recommended. Overall, the risks of identity theft highlight the need for proactive measures.
Why NordVPN is a Smart Choice for Protection
Protecting your online calendar starts with reliable tools like NordVPN, which offers top-tier security features. NordVPN encrypts your internet connection, ensuring that shared calendars remain private from prying eyes. This solution is ideal for anyone navigating the web, as it shields against hackers and data breaches effectively. By using NordVPN, you gain peace of mind knowing your personal information is secure. Moreover, its user-friendly interface makes it accessible for beginners and experts alike. Transitioning to NordVPN means fewer worries about unprotected sharing. It also blocks malicious sites that could target your calendar data. Therefore, it’s a comprehensive defense for your digital life. In conclusion, NordVPN stands out as the best option for safeguarding your online activities. Sign up for NordVPN today and take control of your privacy—protect your calendar and enjoy secure sharing now. This step will enhance your online safety and prevent hidden risks from escalating.
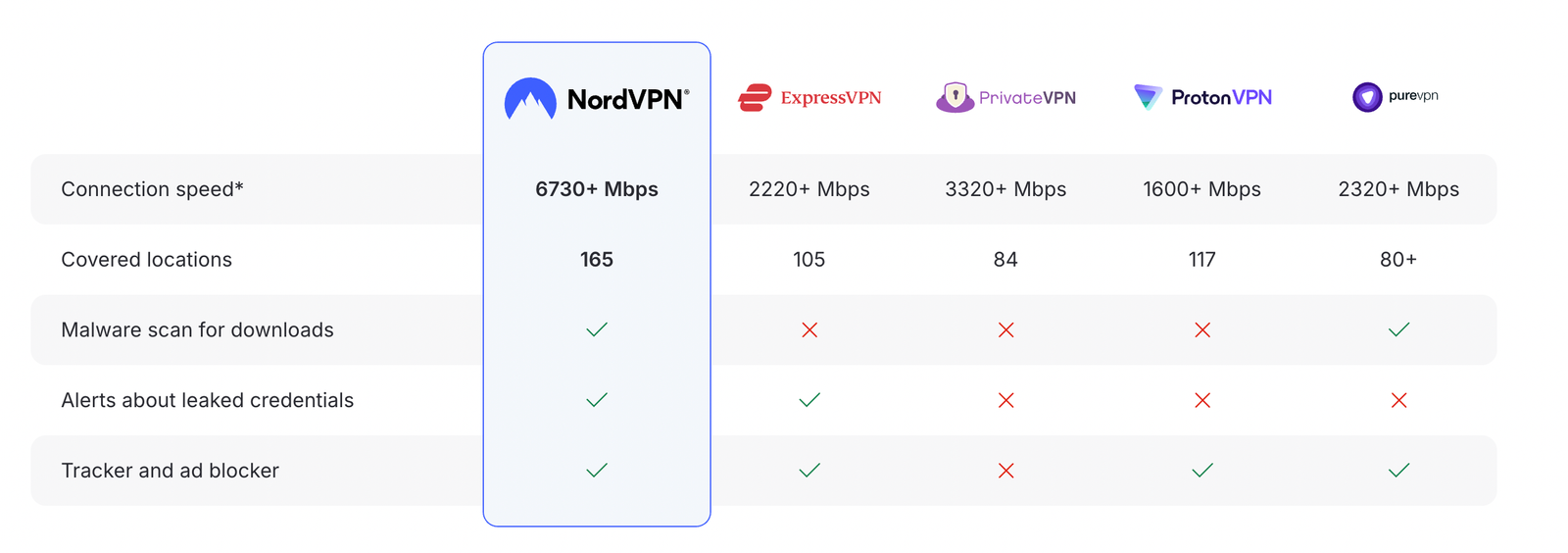
How NordVPN compares to other top VPNs

Disclosure: We earn a commission at no extra cost to you if you make a purchase through links here. This helps support us in creating more content for you. Thank you for your support!