Hidden Risks of Unprotected Online Cloud Storage
In today’s digital world, online cloud storage has become essential for storing files and data. Many people use services like Google Drive or Dropbox without thinking about the dangers. Unprotected cloud storage exposes users to hidden risks that can lead to data loss, theft, and privacy breaches. This post explores these threats and why securing your data matters. Hackers often target weak systems, making everyday users vulnerable. For instance, without encryption, sensitive information like photos or financial details could be accessed easily. SEO experts recommend understanding these risks to improve online safety searches. Moreover, businesses face severe consequences from data exposure. As cloud usage grows, so do the threats from cybercriminals. This discussion aims to educate everyone on protecting their digital assets. Remember, simple steps can prevent major issues. Online storage is convenient but not always safe without proper measures. Keywords like “unprotected cloud storage risks” highlight common concerns in search results. Therefore, let’s dive deeper into these hidden dangers.

The Threat of Data Breaches
Unprotected cloud storage often leads to data breaches. Hackers exploit weak security to steal information. For example, they use phishing attacks to gain access. This exposes personal and business data to theft. Moreover, once breached, files can spread quickly online. Users might lose control of their information forever. Additionally, breaches damage reputations and cause financial losses. Companies have faced millions in damages from such incidents. Transition words help connect ideas smoothly here. Furthermore, common vulnerabilities include unencrypted connections. Attackers target these weak points easily. In fact, studies show breaches are rising yearly. Therefore, understanding breach methods is crucial for protection. Users should know that simple passwords won’t suffice anymore. Hackers employ advanced tools to crack defenses. This paragraph emphasizes the need for awareness. Moreover, everyday activities like sharing files can invite risks. For instance, public links without restrictions are dangerous. They allow unauthorized downloads instantly. Additionally, mobile access amplifies threats due to weaker device security. Users often overlook these factors in daily routines. Transition words enhance flow in this section. Furthermore, the impact includes identity theft and fraud. Victims spend years recovering from such events. Hackers sell stolen data on dark web markets. This creates a cycle of ongoing threats. In addition, businesses deal with regulatory fines for non-compliance. Therefore, preventing breaches starts with better practices. Users must encrypt data and use multi-factor authentication. Moreover, regular updates patch vulnerabilities effectively. This reduces exposure significantly. Hackers evolve tactics, so vigilance is key. For example, ransomware attacks lock files until payment. This adds another layer of risk. Transition words link these points clearly. Furthermore, the frequency of breaches in cloud services is alarming. Reports indicate thousands of incidents annually. Users need to act proactively. In summary, data breaches pose severe threats to unprotected storage. Moreover, adopting safeguards can mitigate these dangers effectively. This discussion highlights real-world examples to educate readers. Hackers target anyone, making preparation essential. Therefore, awareness is the first step toward security.

Risks of Unauthorized Access
Unauthorized access is a major risk in unprotected cloud storage. Strangers can view or alter your files easily. For instance, weak passwords allow intruders to log in. This compromises privacy and security instantly. Moreover, shared accounts heighten these vulnerabilities. Family members or colleagues might expose data accidentally. Additionally, public Wi-Fi networks make access easier for attackers. Users often connect without secure connections. Transition words improve sentence connections here. Furthermore, once inside, hackers can monitor activities in real-time. They steal sensitive information like emails or documents. This leads to identity theft and blackmail. In fact, cases involve celebrities whose clouds were hacked. Therefore, protecting access points is vital. Users should implement strong authentication methods. For example, biometric locks add an extra barrier. Moreover, session timeouts prevent prolonged exposure. Unauthorized access often stems from human error. People reuse passwords across platforms. This creates entry points for cybercriminals. Additionally, forgotten logouts on shared devices invite risks. Hackers exploit these oversights quickly. Transition words help tie ideas together. Furthermore, the consequences include legal issues and emotional distress. Victims feel violated and powerless. Businesses lose customer trust from such breaches. In addition, regulatory bodies investigate these incidents. Therefore, prevention involves regular security audits. Users must review permissions frequently. For instance, revoke access for former employees promptly. Moreover, encryption at rest and in transit secures data layers. This paragraph explores access risks in depth. Hackers use sophisticated tools like keyloggers. They capture login credentials undetected. Additionally, malware infects devices through cloud links. This spreads access to other systems. Transition words enhance readability here. Furthermore, the rise of remote work amplifies these threats. Employees access clouds from various locations. Unsecured networks become gateways for attacks. In fact, statistics show a surge in incidents post-pandemic. Therefore, companies need robust policies. Users should educate themselves on best practices. Moreover, using VPNs encrypts connections effectively. This blocks unauthorized eyes from viewing data. In summary, access risks are pervasive in unprotected storage. Moreover, proactive measures can safeguard your information. This section underscores the importance of vigilance.

Legal and Compliance Dangers
Unprotected cloud storage brings legal and compliance dangers. Users might violate data protection laws unintentionally. For example, GDPR fines target non-compliant storage. This affects individuals and organizations alike. Moreover, failing to secure data leads to lawsuits. Victims sue for privacy invasions frequently. Additionally, international transfers complicate compliance further. Different countries have varying regulations. Transition words connect these concepts smoothly. Furthermore, businesses face audits and penalties for breaches. Non-compliance can halt operations temporarily. In fact, examples include major corporations paying hefty fines. Therefore, understanding legal risks is essential. Users must ensure their storage meets standards. For instance, implement data residency requirements. Moreover, encryption helps with compliance obligations. Legal dangers often arise from poor data handling. Storing sensitive info without consent is illegal. This exposes users to investigations. Additionally, lost data due to hacks triggers reporting mandates. Companies must notify authorities promptly. Transition words aid in flowing transitions. Furthermore, the costs include legal fees and settlements. Victims seek compensation for damages. In addition, reputation harm affects future opportunities. Therefore, proactive compliance is key. Users should use tools that track access logs. For example, audit trails prove accountability in courts. Moreover, regular training reduces human errors. This paragraph delves into compliance issues. Hackers exploit non-compliant systems for leverage. They demand ransoms using stolen data. Additionally, governments investigate breaches rigorously. This adds pressure on affected parties. Transition words enhance the structure here. Furthermore, small businesses are not exempt from these risks. They often lack resources for compliance. In fact, statistics reveal higher failure rates among them. Therefore, affordable solutions are necessary. Users can adopt automated compliance tools. Moreover, consulting experts ensures adherence. In summary, legal dangers are significant with unprotected storage. Moreover, staying compliant protects against severe outcomes. This discussion highlights real implications for all users.
Why NordVPN is Your Best Choice for Security
Protecting your cloud storage starts with reliable tools like NordVPN. This service offers robust encryption to shield data from hidden risks. For instance, it prevents breaches and unauthorized access effectively. Moreover, NordVPN ensures compliance with global standards. Users enjoy peace of mind knowing their files are secure. As we’ve discussed, unprotected storage leads to serious threats. Therefore, choosing NordVPN counters these dangers smartly. It provides features like a no-logs policy and fast connections. This makes it ideal for anyone handling sensitive information. Transition words link points here. Furthermore, its user-friendly interface suits beginners and experts. NordVPN is a good choice because it combines affordability with top-tier protection. For example, it blocks malware and trackers seamlessly. Additionally, the service supports multiple devices. This covers all your cloud needs comprehensively. In conclusion, NordVPN stands out as the ultimate solution. It relates directly to the risks outlined, offering comprehensive defense. Why wait when your data is at stake? Take action now and sign up for NordVPN to secure your online storage today. Boost your safety with this trusted provider. Start protecting what matters most immediately.
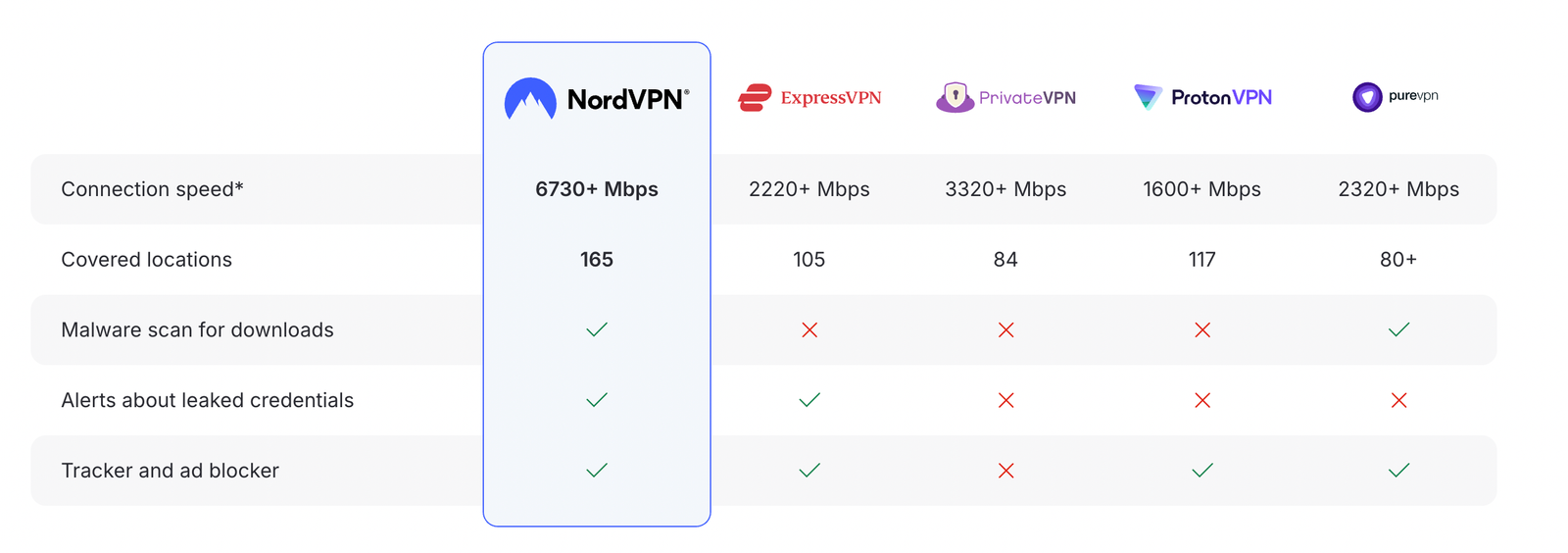
How NordVPN compares to other top VPNs

Disclosure: We earn a commission at no extra cost to you if you make a purchase through links here. This helps support us in creating more content for you. Thank you for your support!